How to use Intune to manage Secure Boot Certificates

June 2026 should be marked in your calendar not for your summer holiday, but the fact that the Secure Boot Certificates will expire! These certificates are from 2011 and June 2026 marks the expiration date. When your Windows devices are managed with Intune, you can use Intune to handle the update process. But there are some caveats find out which!
11-03-2026 Updated with the Secure Boot Status Reports!
Secure Boot Certificates
Microsoft has released different articles about the Secure Boot update procedure. I won't go in to detail about Secure Boot and the techniques, but I will described the steps you can take in Intune to update the certificates, these steps are also mentioned in the Playbook that Microsoft has released, make sure you read this playbook, it's listed in the documentation in this post
Secure Boot is a UEFI firmware security standard that ensures a computer boots using only software trusted by the manufacturer. Windows 11 requires that Secure Boot is enabled, so most of the organizations will have secure boot enabled on their Windows devices. Many devices manufactured after 2024 will already have the new 2023 certificates, but make sure you will have the latest firmware update from your OEM the make sure your device is compatibel.
Intune Create Policy
Create a configuration policy to handle the update proces for managed devices.
From the Intune portal head-over to
Devices > Configuration and make a new settings catalog profile
Search for Secure Boot in the Setting Picker and select the three settings.
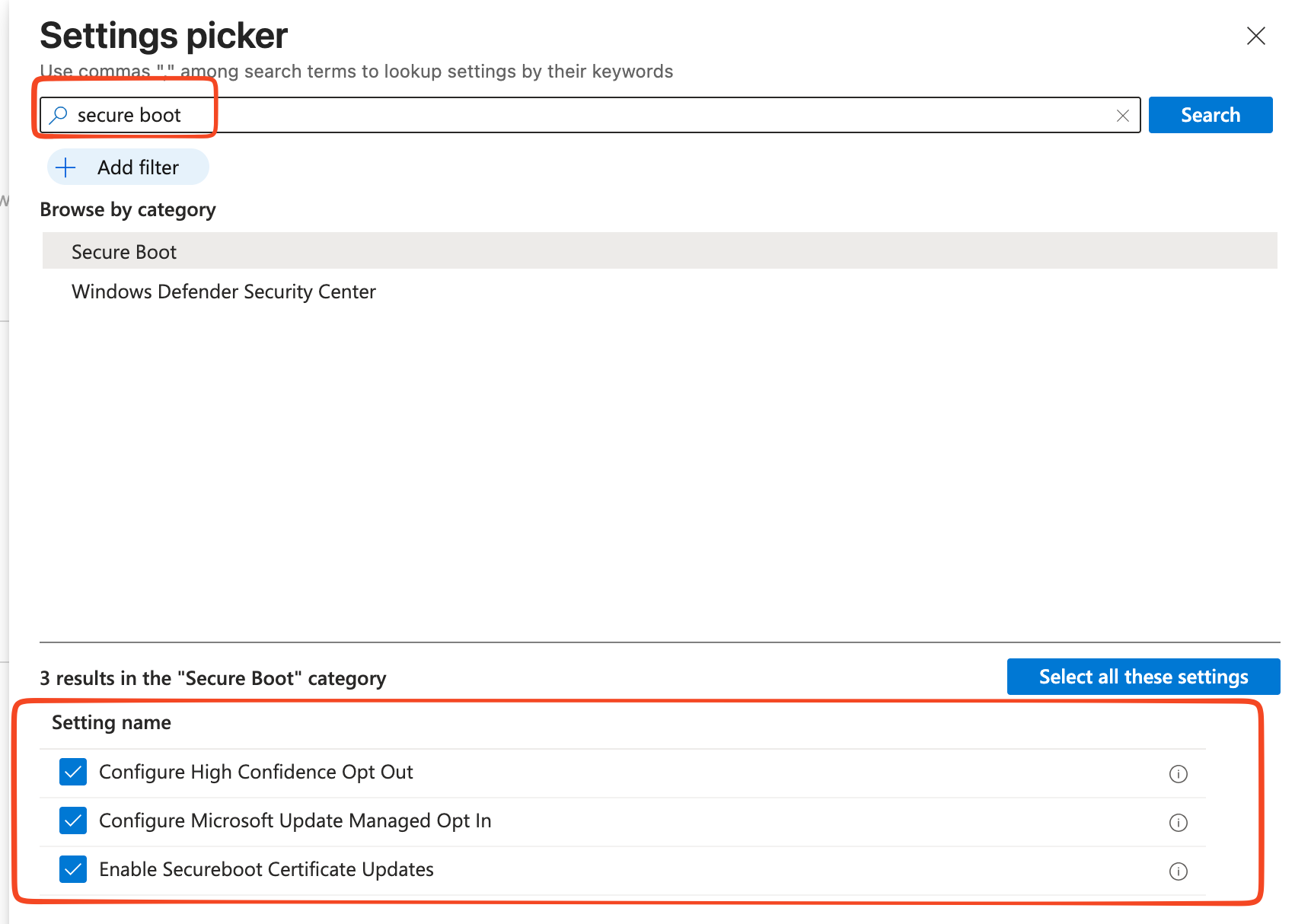
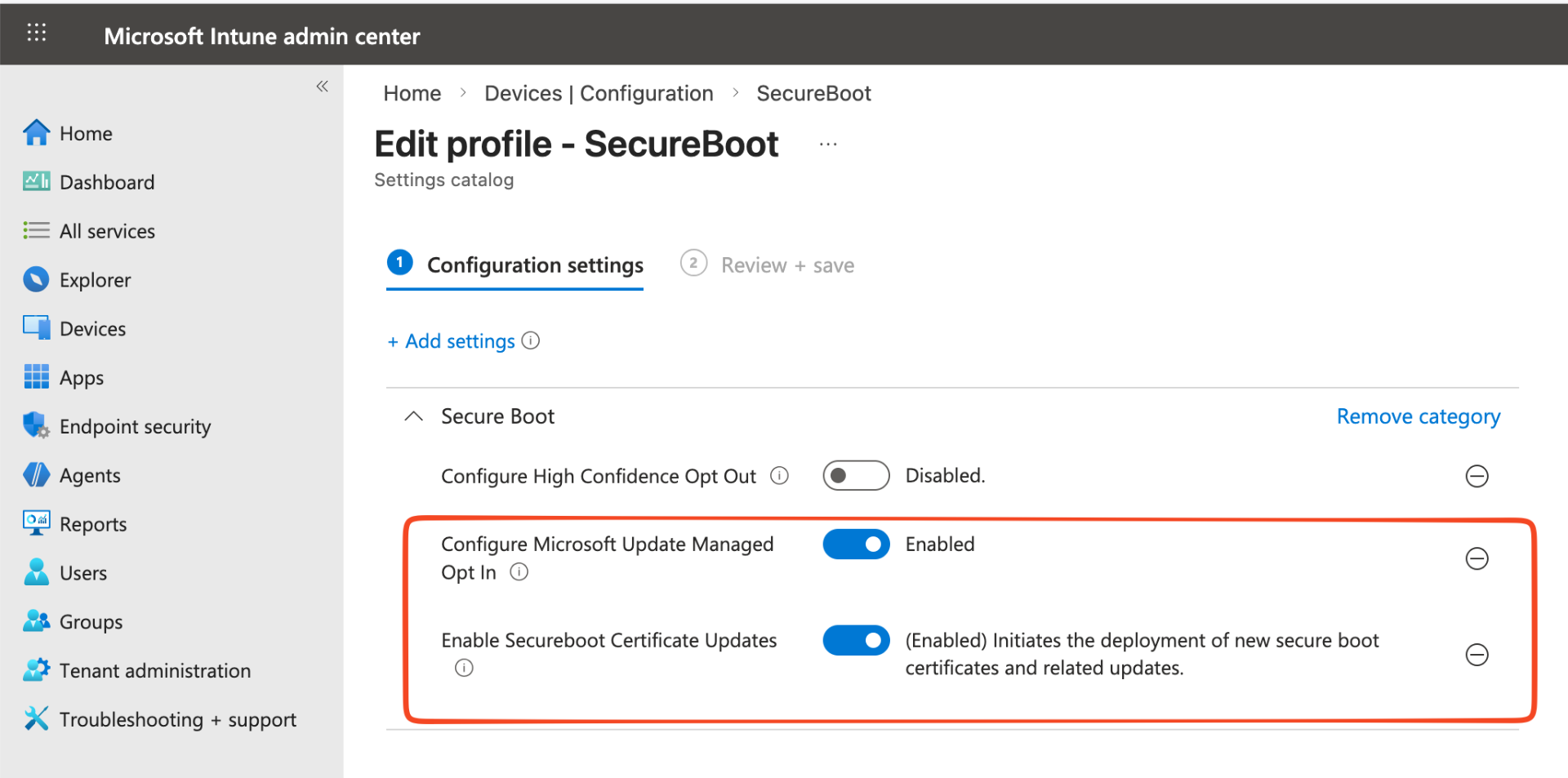
Enable the settings; Configure Microsoft update Managed Opt in and Enable Secureboot Certificate Updates. Assign the profile to the corresponding group.
Intune Check Policy
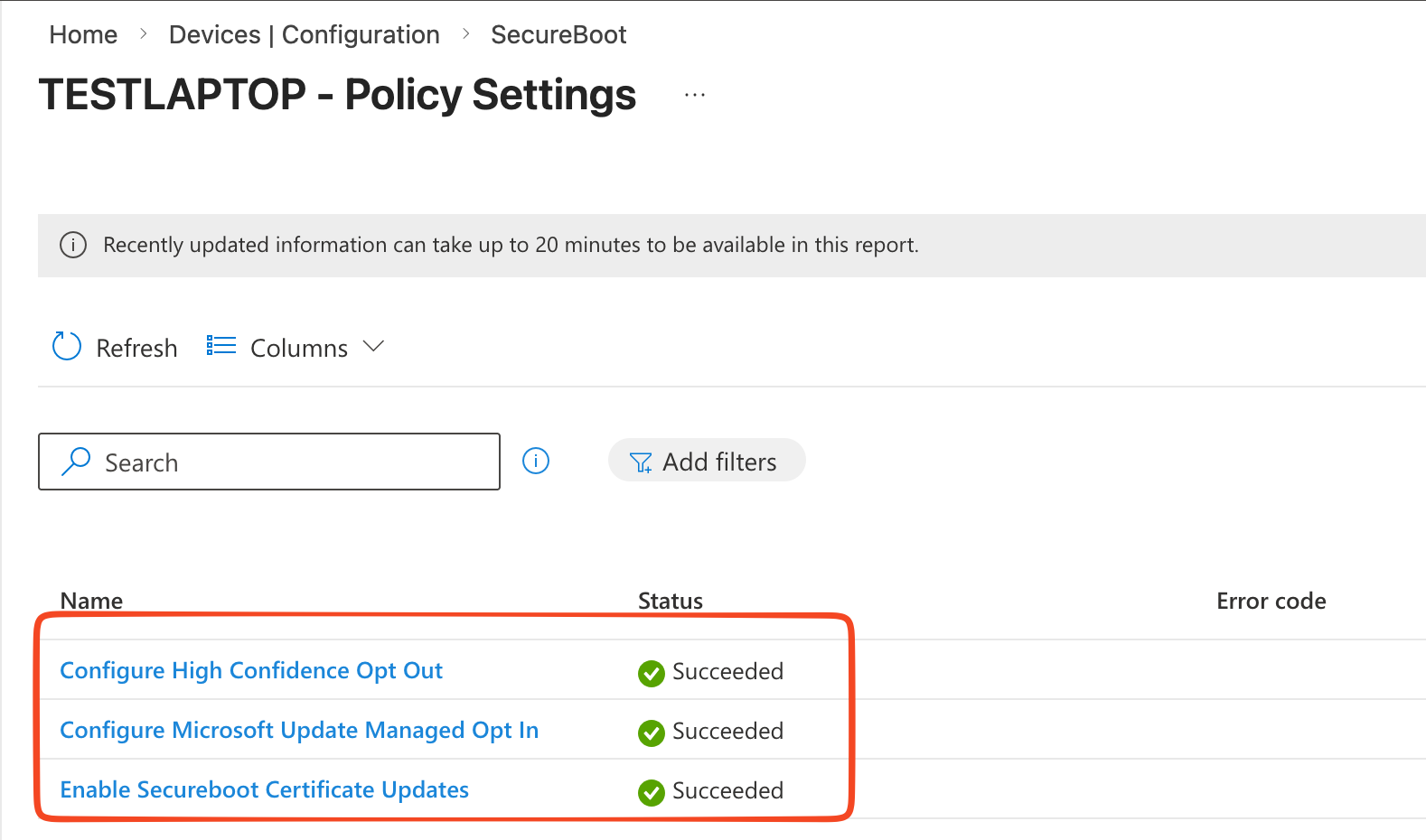
Now that we have set the policy and when the device has synced we can check the policy and the device to make sure the settings are applied.
The option for the Secure Status Report is available, read on the find the steps to see or activated this report.
We can see if the policy has been set correct, head over the policy and view the report.
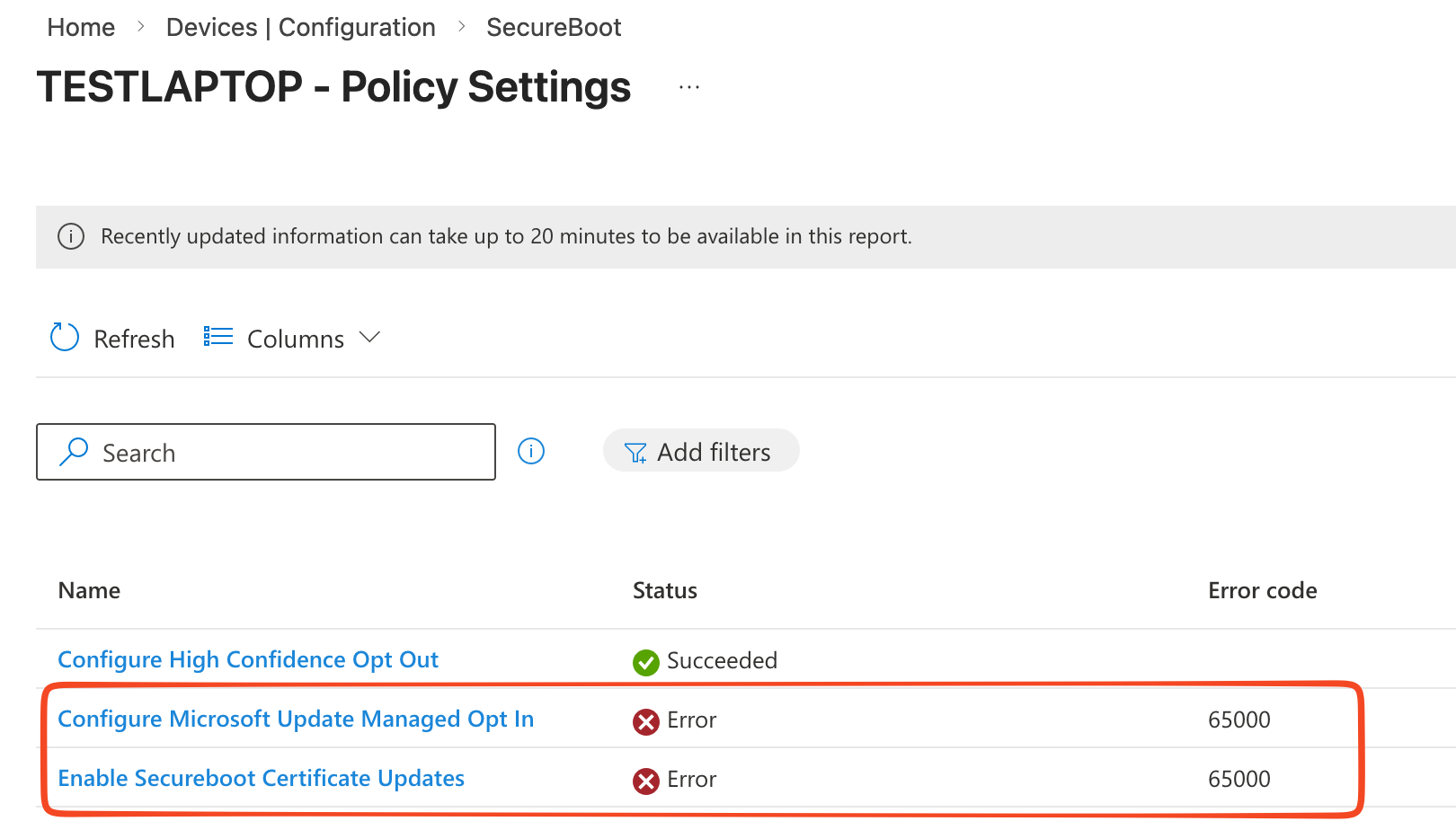
When you encounter the famous 65000 error no worries. This is a know issues and Microsoft has documented the resolution for this!
Perform the Clipdls.exe removesubscription and cliprenew.exe commands.
There is a good chance that you will get an error 65000. Microsoft has adressed this as an know issues and in the community you will find blogpost about this. It has to do with a license issues, we can resolve this by preforming the following commands on the device as the user:
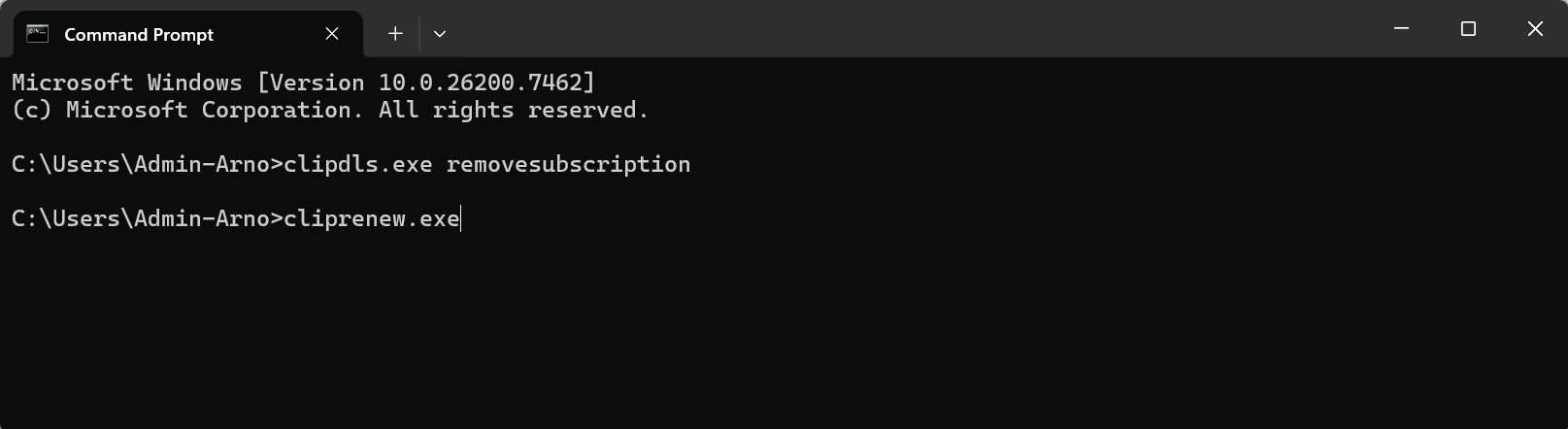
After running this command on the device and a reboot the policy status is shown correctly.
Check Device
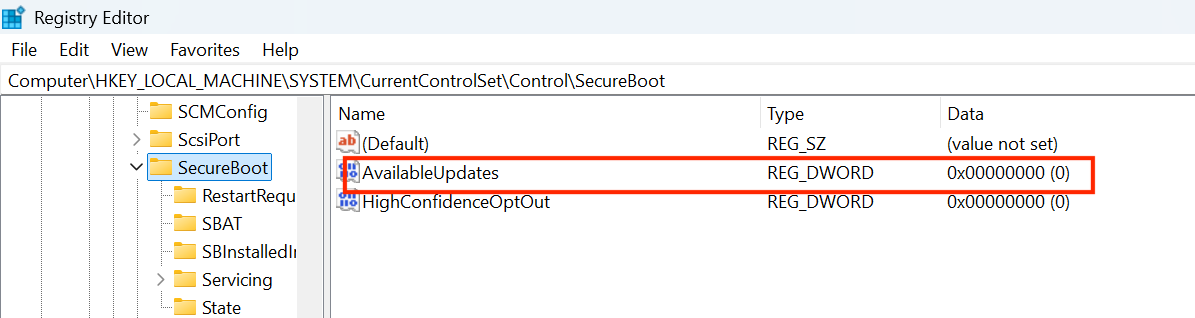
As mentioned before the OEM manufacturer will release firmware updates tho make sure the devices is compatibel. When we have set the policies we can check the device for the correct settings and it the update is performed. Open the registry and navigate to the following key:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecureBoot
We can see that there isn't a update available yet, see documentation in this blog for the data details for the reg keys.
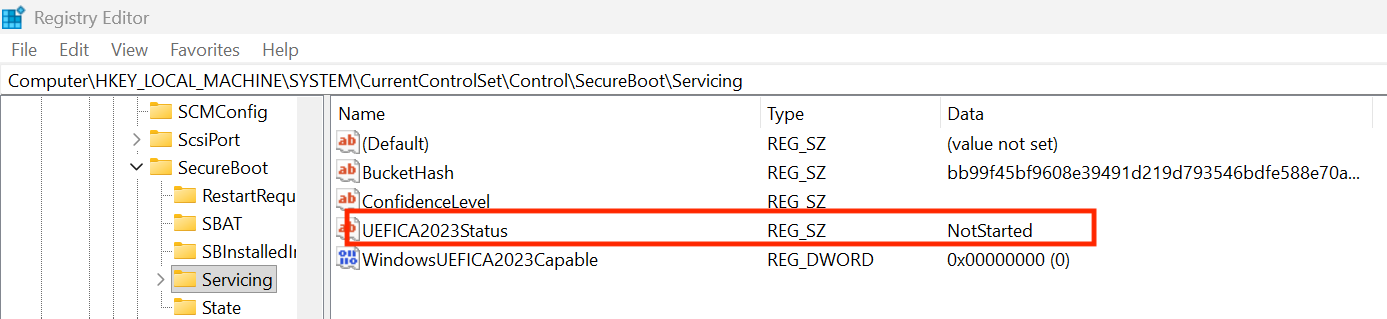
We can check the update status in the following key.
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecureBoot\Servicing
The update hasn't started yet, see documentation in this blog for the data details for the reg keys.
Check Device after update and reboot
On my device there was a firmware update and the KB5077181 update to prepare the device for Secure Boot updates. After these updates and a reboot the register keys changed.
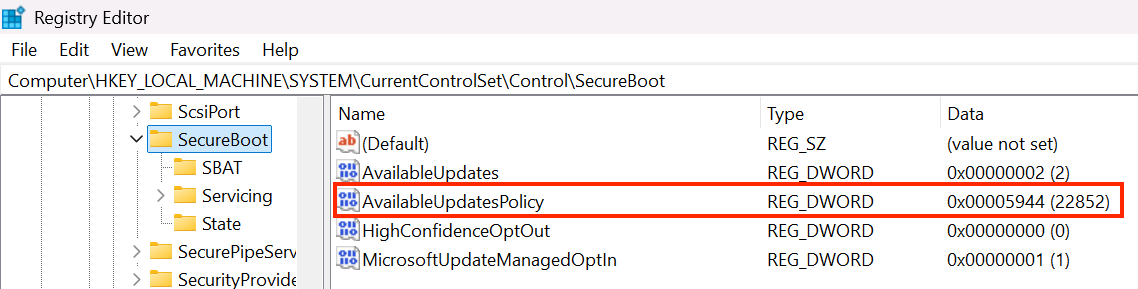
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecureBoot
The key AvailableUpdatesPolicy was changed to 0x5944 meaning it will deploy all needed certificates and update to the PCA2023 signed boot manager.
The update status key also changed;
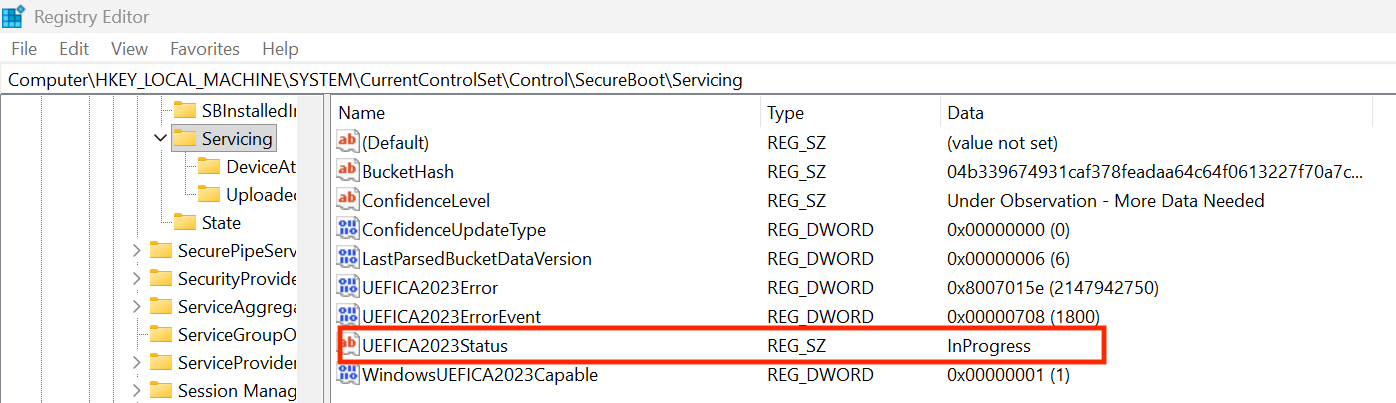
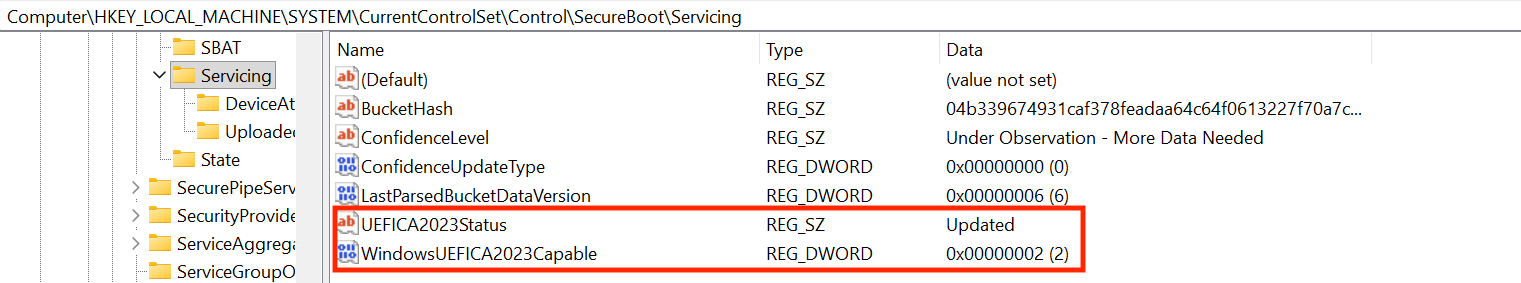
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\SecureBoot\Servicing
The UEFICA2023Status has changed to InProgress
We can also check the eventviewer to check if the update is succesfull.
- Event 1808 for success
- Event 1801 for error
On my device event 1801 is listed, 1808 not.
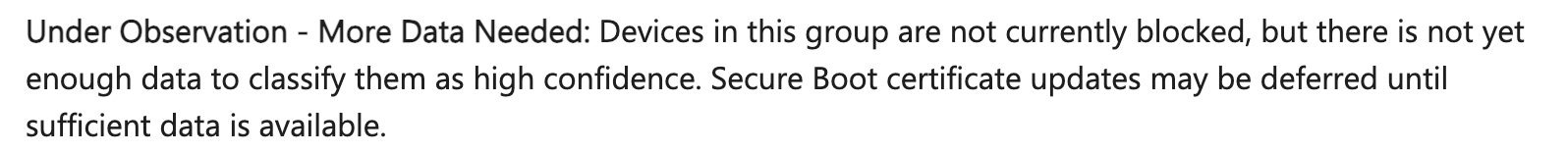
Message: Under Observation - More Data Needed
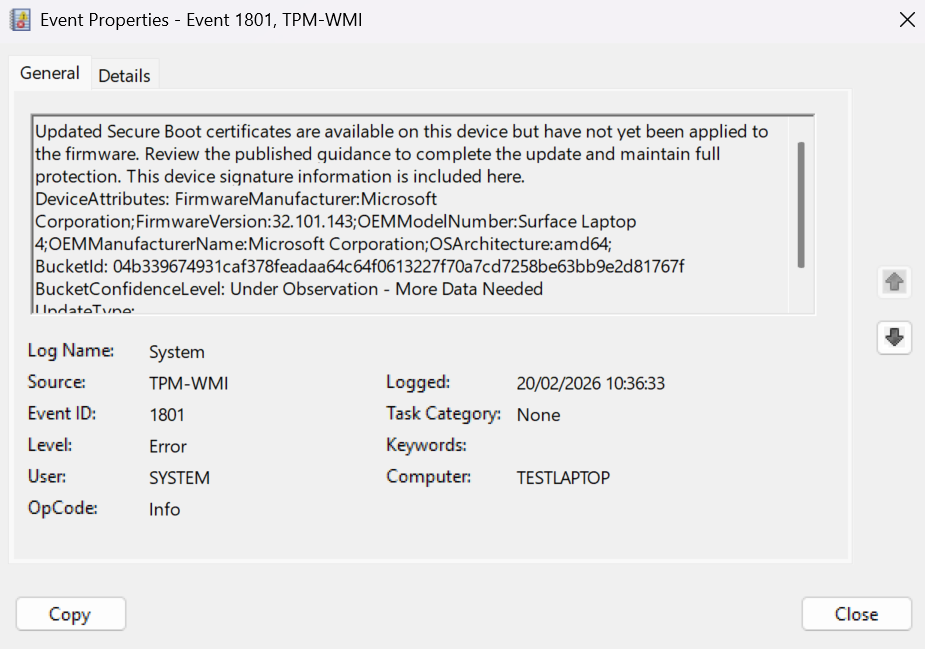
Looking in the documentation this is mentioned for the error.
When running the following PowerShell command, the results are shown correctly.
You can use the following command to check:
([System.Text.Encoding]::ASCII.GetString((Get-SecureBootUEFI db).bytes) -match 'Windows UEFI CA 2023')
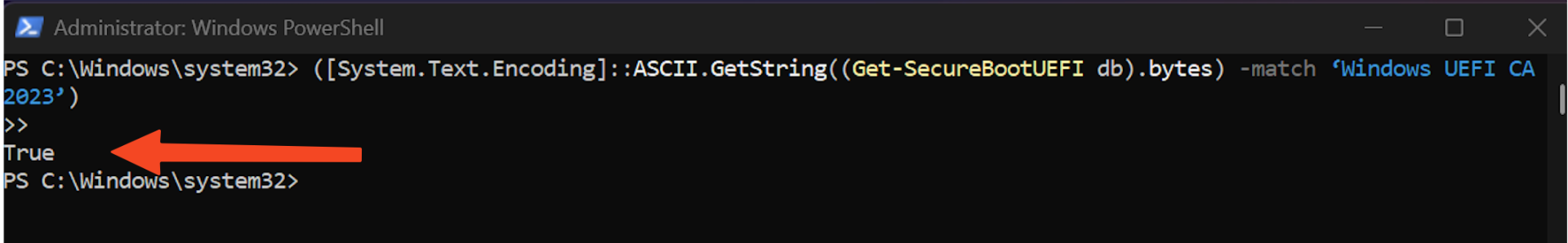
After a couple of minutes and an reboot the registry value has changed
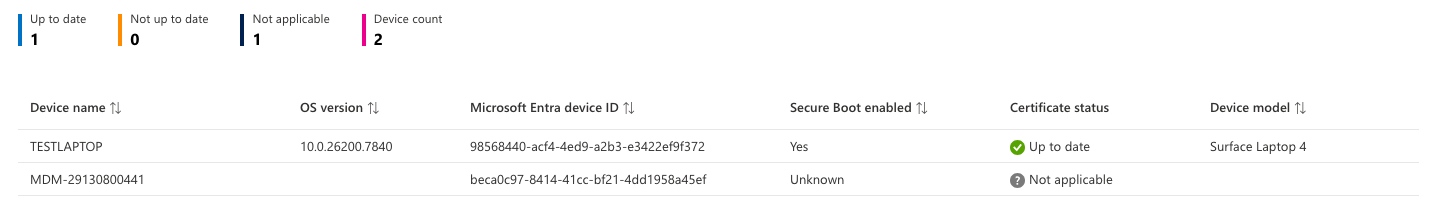
Secure Boot Status Report
We can use the pre-built Secure Boot status report to determine the status of our devices. These reports provide information about Windows Autopatch. If you don't use Autopatch, you must first enable it to view the report/
From the Intune portal head-over to:
Tenant Administration > Tenant management
Check the status of the Client broker and install the client if necessary, upon installation it can take some hours (days) before the report become available.
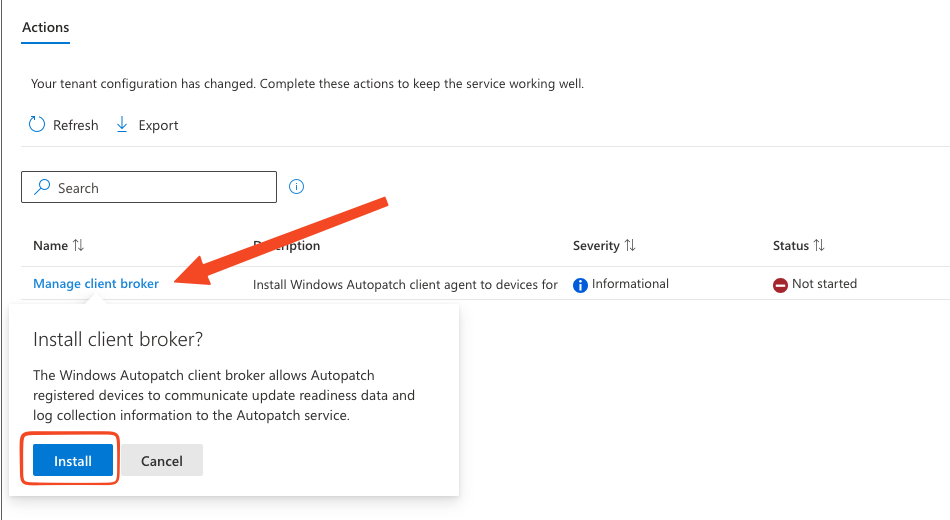
If you have installed the client, we can see the report.
From the Intune portal head-over to:
- Reports
- Windows quality updates
- Reports
- Secure Boot status
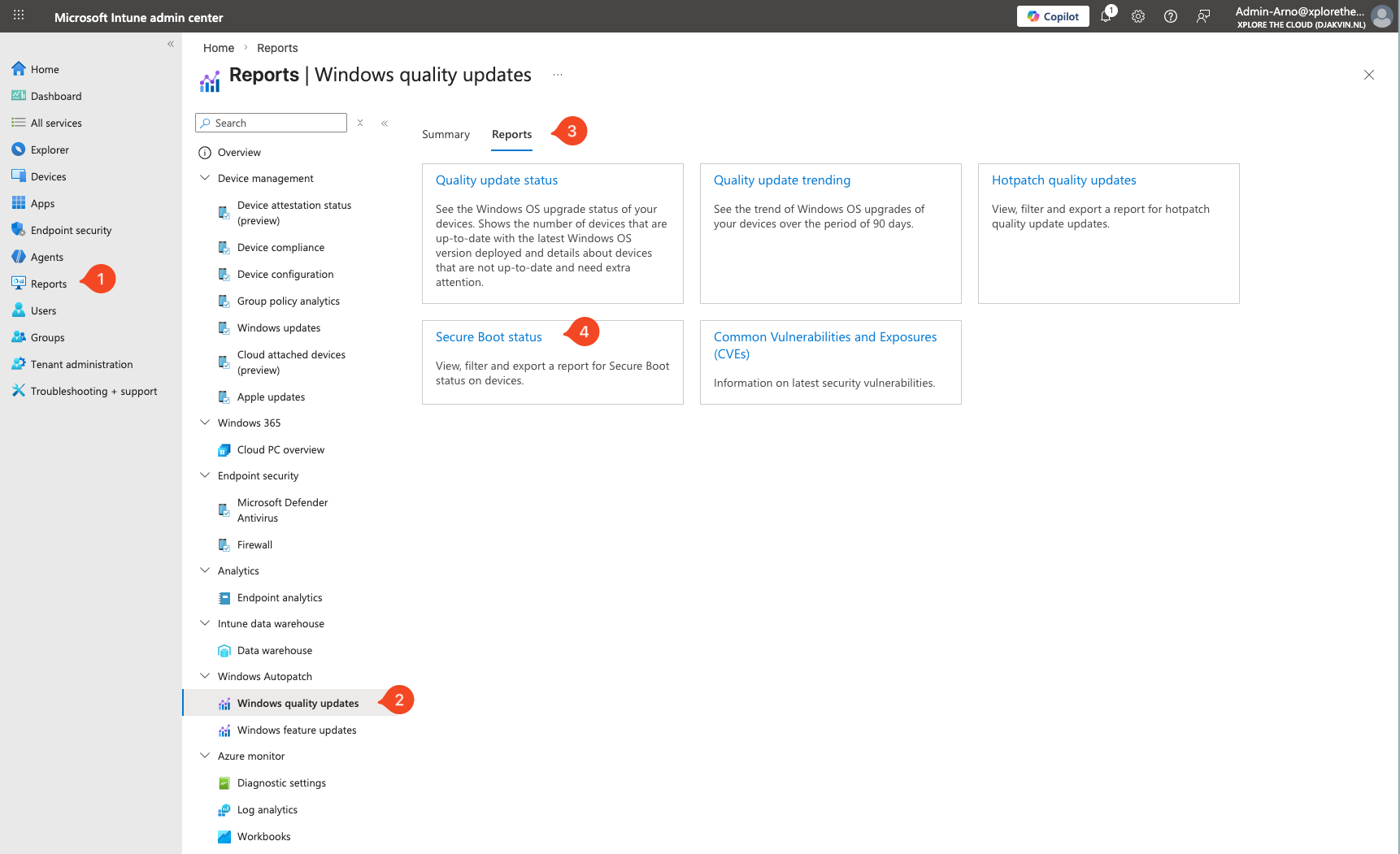
When you select the Secure Boot status report, the report wil open an show you the status, from here we can find out
- Which devices have Secure Boot enabled?
- Which Secure Boot-enabled devices are fully up to date?
- Which Secure Boot-enabled devices need certificate updates?
Intune Proactive Remediation for Detection
We can also use Proactive Remediation to monitoring Secure Boot certificate proces as listed in the steps above. This is more convenient for managing a fleet of devices. Microsoft has released a detection script we can use to check if the correct registry keys are set, check the eventlog for 1801 and 1808 and WMI / CIM for the OS version, last boot time, and baseboard hardware info. Make sure that your license support Proactive Remediation when you want to enable this script. See the documentation in this post for the script that Microsoft has released.
From the Intune portal head-over to
Devices > Scripts and Remediations and create a new remediation policy.
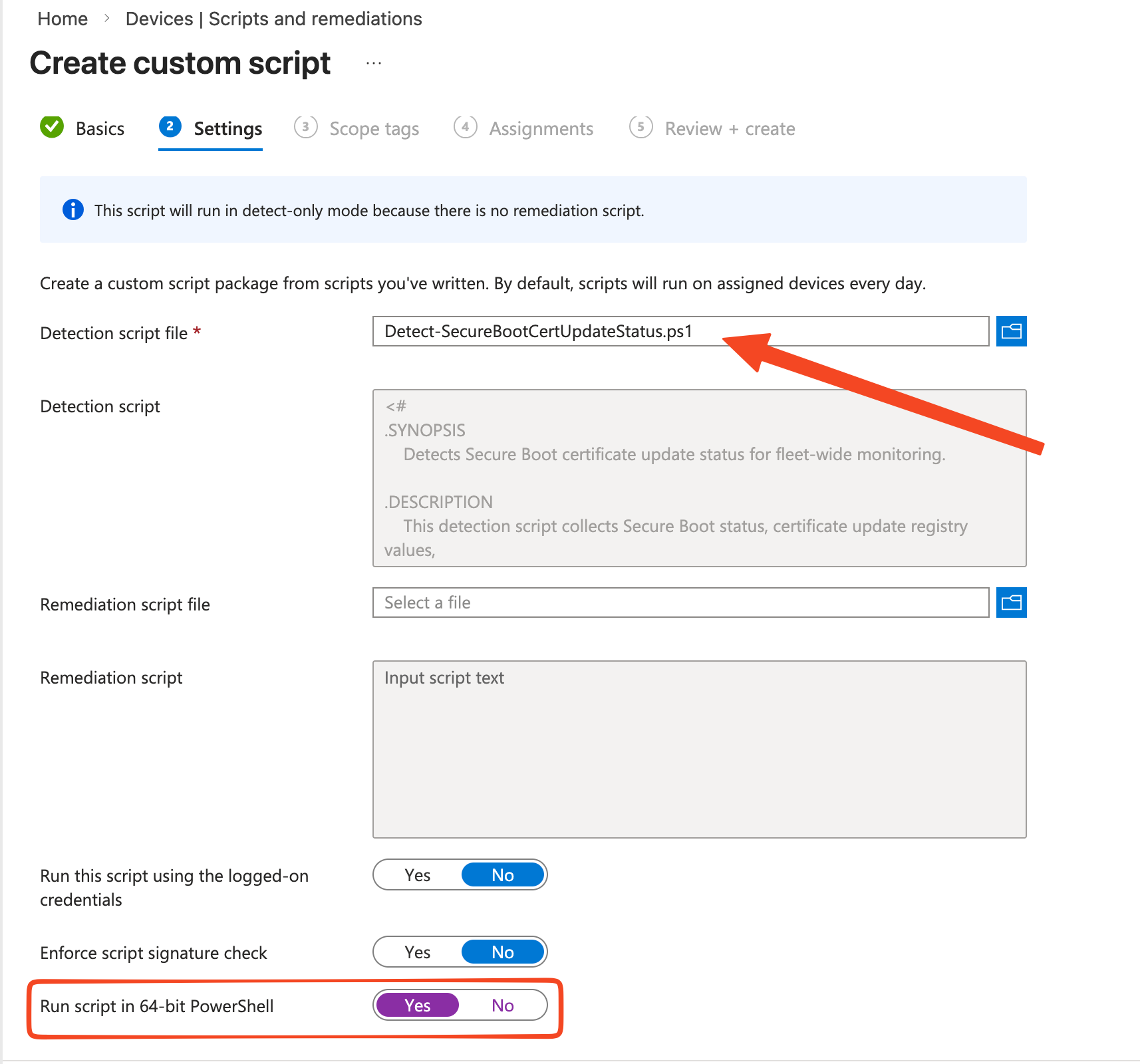
Make use of the script that Microsoft has released. There is no need for a remediation file, it will only detect so we can monitor it. Make sure the script can run in 64 bit Powershell. Assign the policy to your devices.
On the Device Status we can monitor the status of our devices
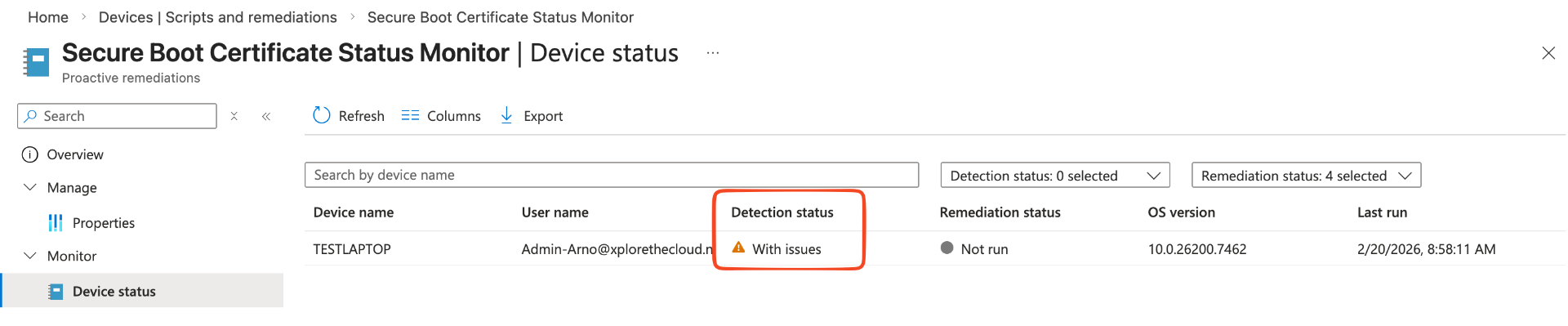
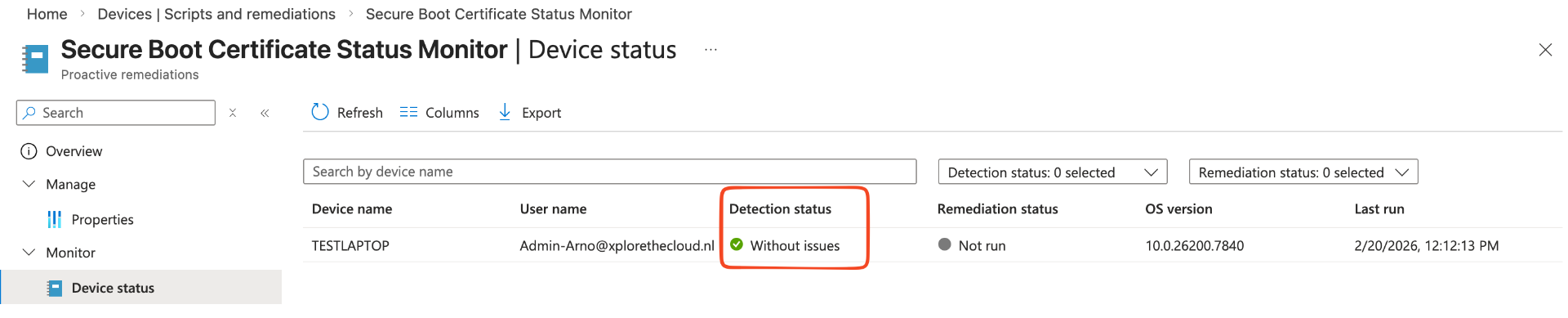
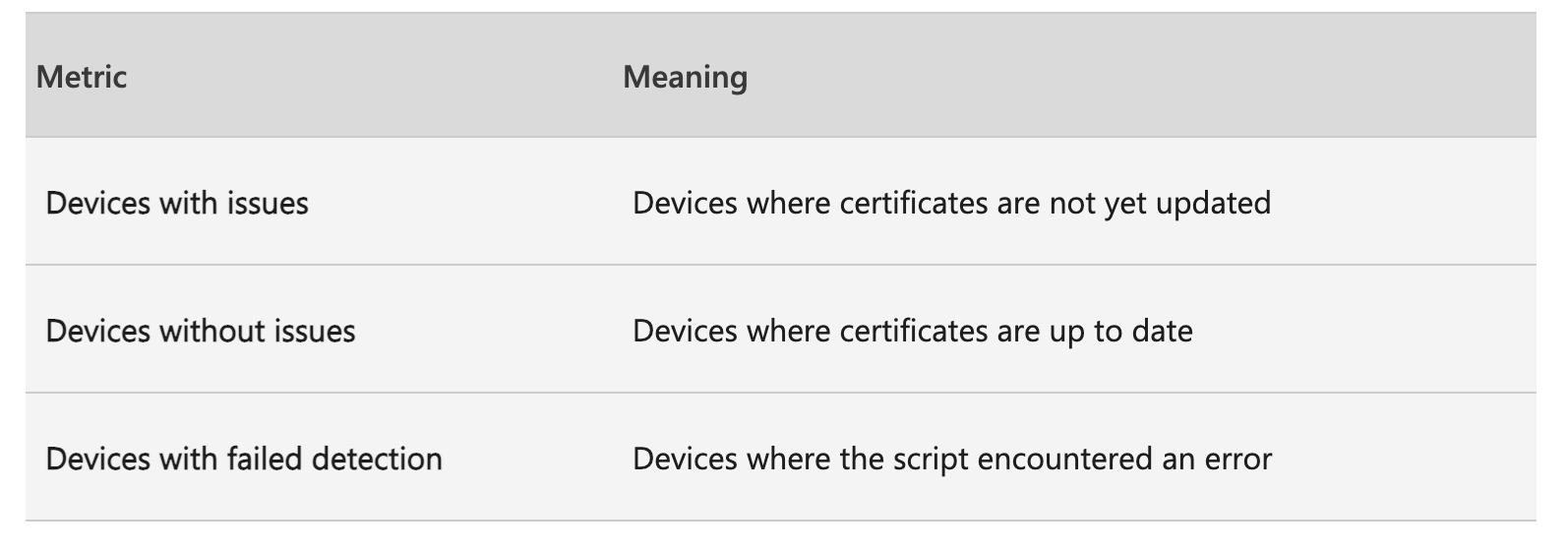
Use the following metrics to determine if the status is correct, in the first example the device hasn't updated the certificates, in the second the device has updated the certificates
Recap
June is approaching quickly, so it is important to start monitoring and updating Secure Boot certificates. Use Intune to deploy the required policy to Windows devices. With the Secure Boot Reports in place when can find out the status of our devices. Microsoft also has released a detection script to get logging in a different way. Updating the certificates can lead to various errors, so review the playbook and documentation in advance. Community blogs and scripts are also available and help achieve the same goal of updating the expired certificates.
