Safeguard your Tokens for macOS using Intune & CA

Token theft, also known as session hijacking, has become a primary attack vector. These attacks can bypass Multifactor Authentication (MFA) prompts, making it essential to protect credentials and, in turn, the tokens themselves. On Windows devices , several techniques are available, such as Windows Hello for Business (WHfB) with Conditional Access. But how can macOS devices be protected? Read on to find out.
macOS Platform Single Sign On (PSSO)
The first step to protect our macOS devices is to onboard then into Microsoft Intune. With the macOS devices onboarded into Microsoft Intune we can make use of the Platform Single Sign On (PSSO) support. PSSO isn't a new feature, it became General Available in Augustus 2025 and with PSSO we can make use of the Microsoft Entra ID credentials for Single Sing On.
PSSO can be configured with the following authentication methods:
- Password
- Smartcard
- UserSecureEnclave Key
I will not go into detail about the functions of PSSO, but I will describe the steps to make the configuration policy and to make use of one particular setting, Secure Enclave.
Read the documentation below the find out more about PSSO and the requirements. I've written a blog a time ago about onboarding a macOS devices with the company portal and making use of PSSO, this blog is also listed in the documentation.
Secure Enclave
According to the Microsoft Documentation, Secure Enclave in PSSO makes use hardware bound cryptographic keys, It doesn't use the Microsoft Entra credentials to authenticate the user to apps and websites. Its considered password-less and meets phish-resistant multifactor (MFA) requirements. It's the Windows Hello for Business but for macOS.
So summarized Secure Enclave in PSSO is a essential step for safeguarding our tokens on macOS.
To make use of Secure Enclave we need to make an configuration profile for macOS. Is this profile you can make the necessary settings for a PSSO configuration, in this blog we will focus for the use of Secure Enclave setting.
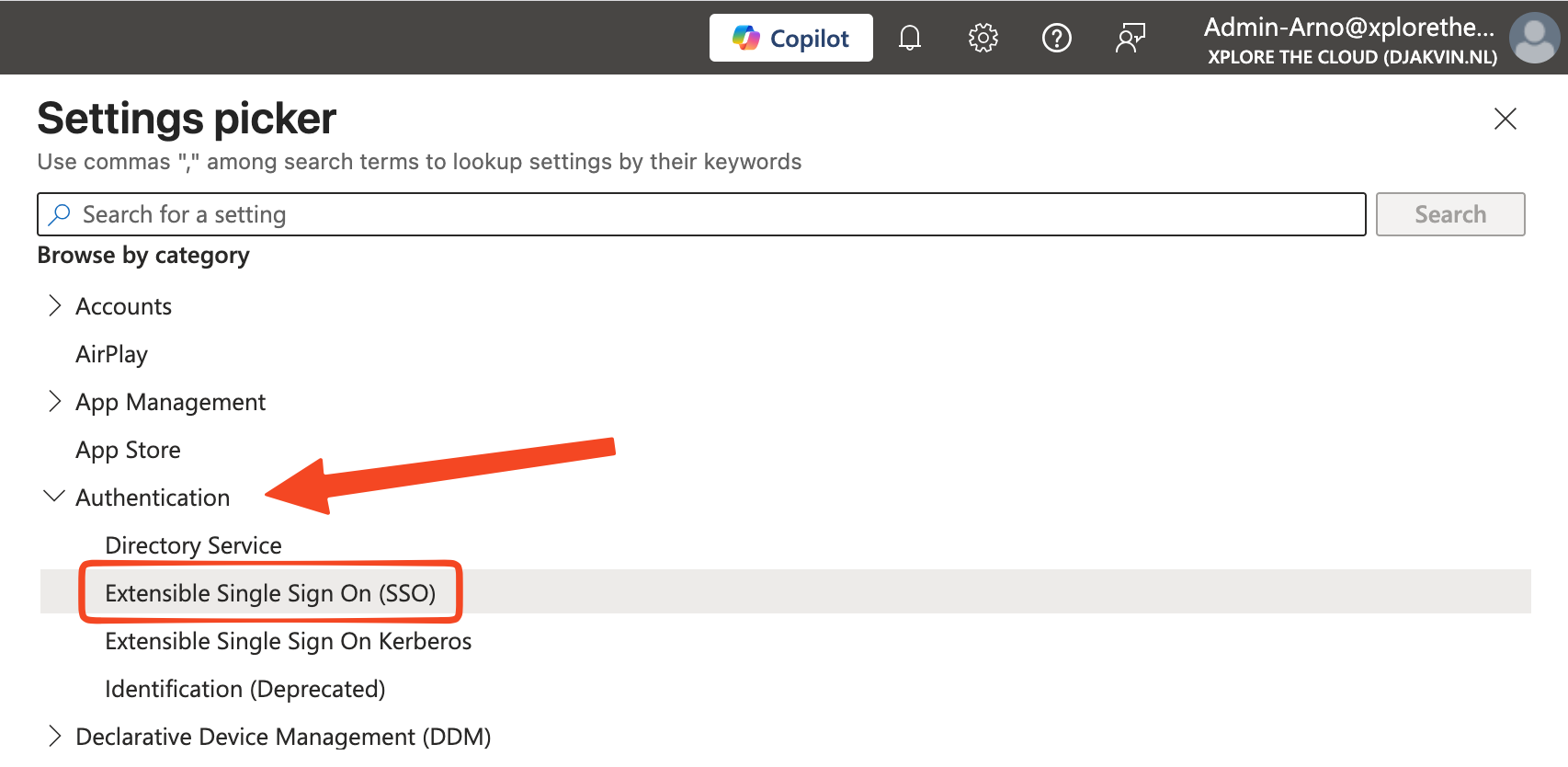
From the Intune Portal:
Devices > macOS > Configuration
Create a Policy from the Setting Catalog and use Authentication, expand the Extensible Single Sign On (SSO) node.
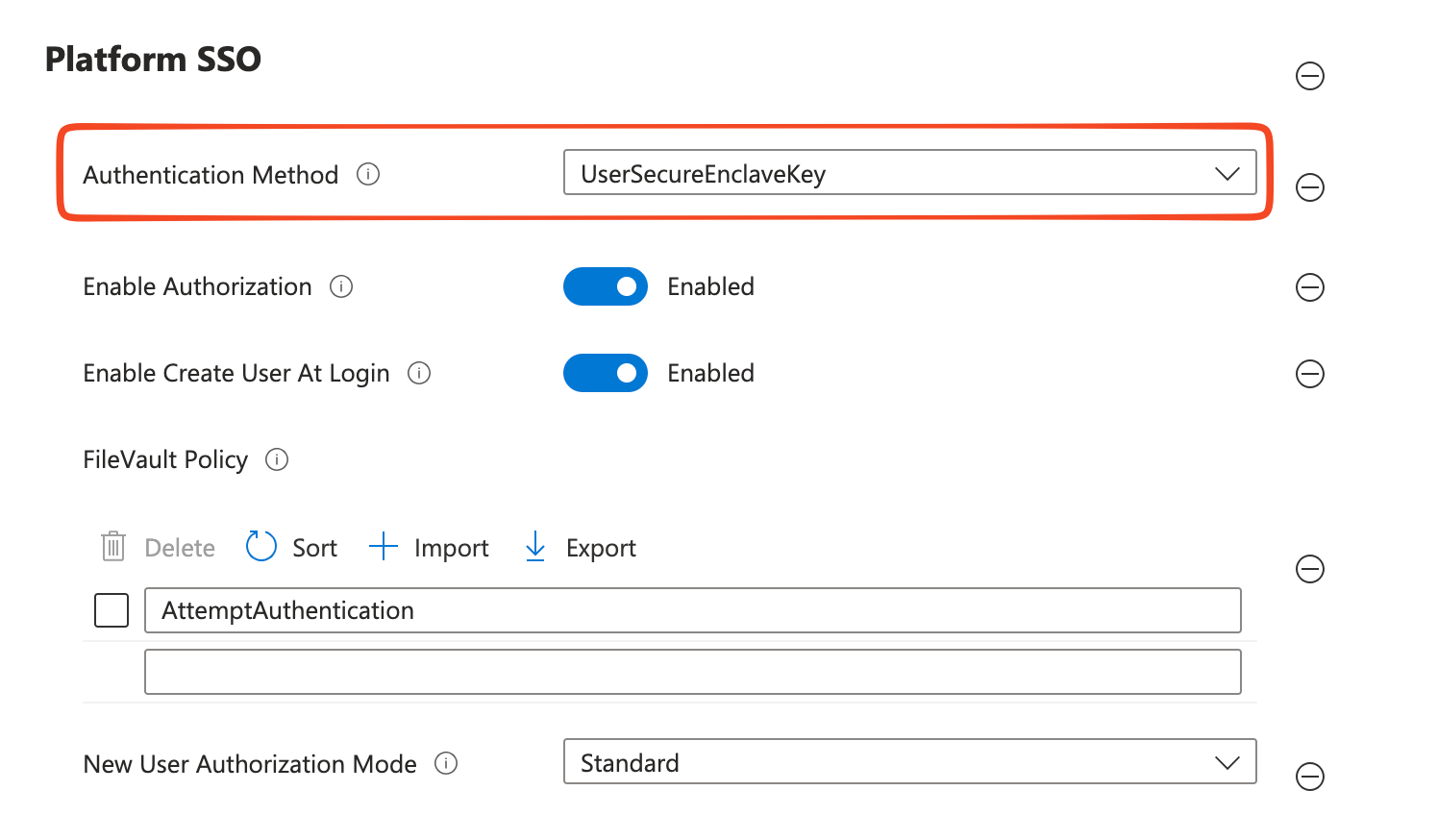
Make the necessary settings for a correct PSSO configuration, use the Microsoft Documentation our my previous blog listed below to find out those setting for PSSO.
In this blog post we focus on the setting in the Platform SSO section, Authentication Method, select the UserSecureEnclaveKey option.
Check device for Secure Enclave
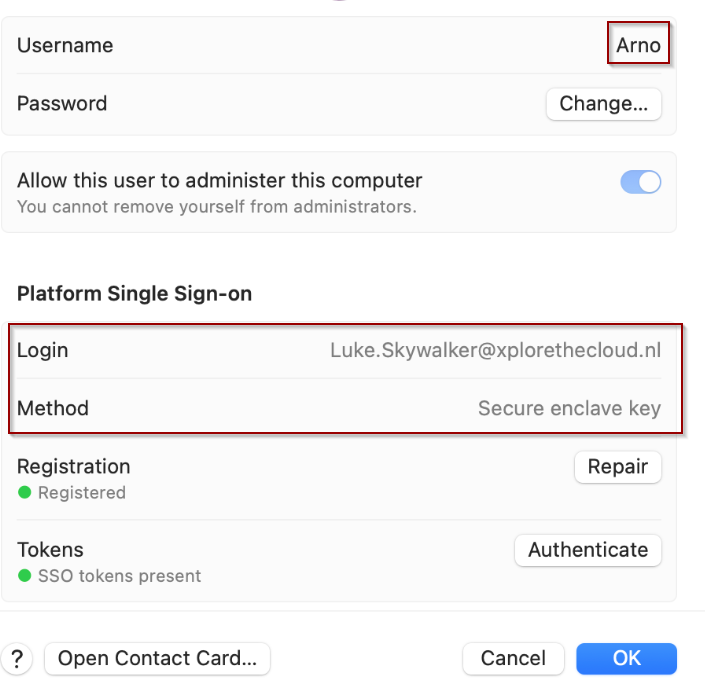
Registration of the PSSO settings differs from the device registration proces. Onboarding can be done manual of through an Automated Device Enrollment (ADE) for macOS. Either way, when the configuration profile is loaded on the macOS device we can check the macOS device for the Secure Enclave setting:
Form macOS device
Settings > Users & Groups
Select the information icon listed next to the local user, we can see that the PSSO login is using Secure enclave key
Force Token Bound on macOS device
Now that we have configured the Secure Enclave method, which meets the phish-resistant multifactor (MFA) requirements, we wan't to make sure the this setting is also required when we authenticate to the Microsoft Services. This way we make sure that only devices are used where the logon credentials are bound to the device.
Conditional Access now supports Token Bound Protection for macOS, it is in public preview.
From the Intune Portal:
Endpoint Security > Conditional Access > Policies
Create a new Conditional Access rule, or change a existing rule which requires Token Bound Protection for Windows.
For macOS the following services are supported:
- Exchange Online
- SharePoint Online
- Microsoft Teams
On Windows, enforcement is also supported for:
- Azure Virtual Desktop
- Windows 365
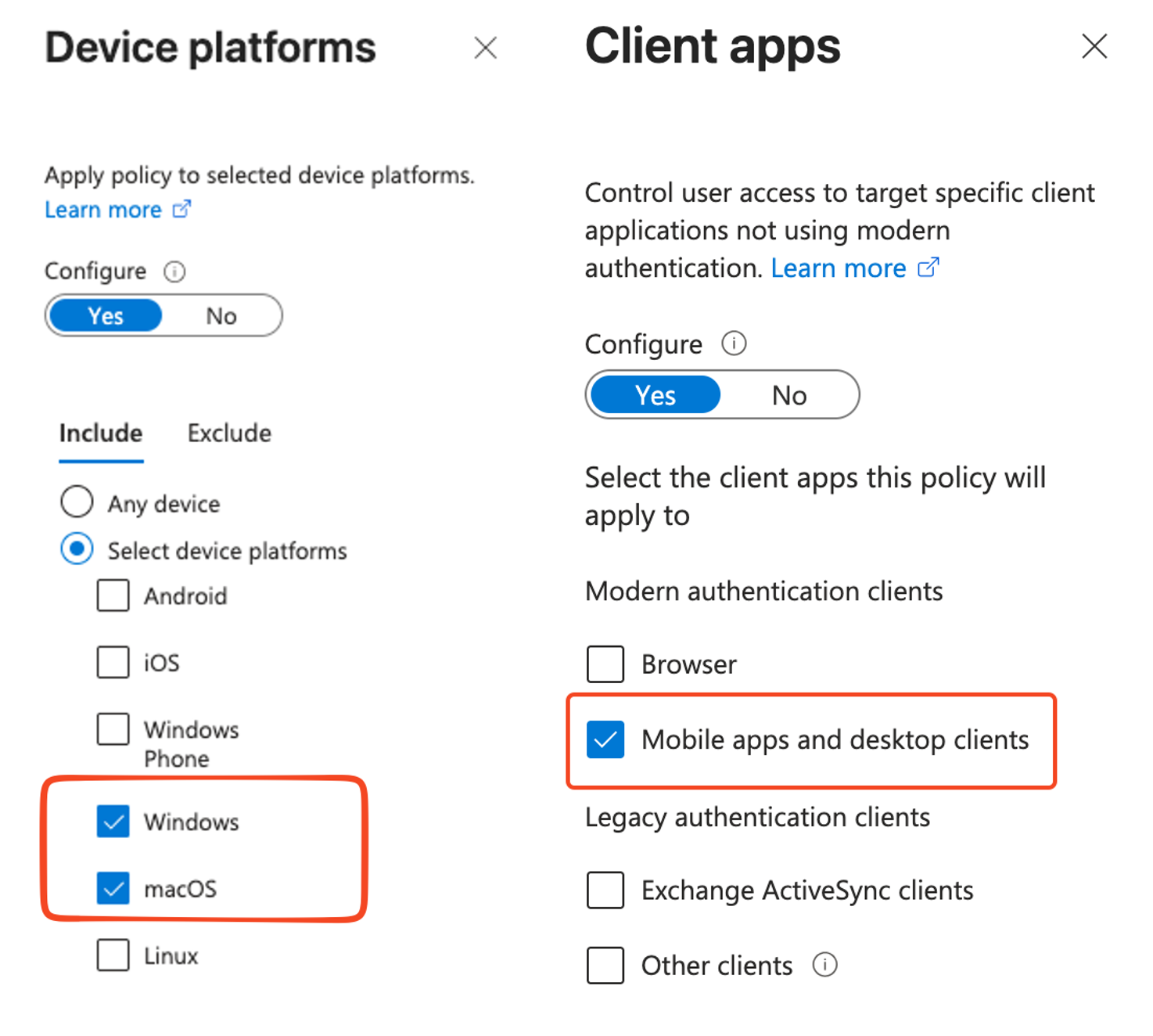
Select the resources, (see above for supported services). Select the platform, in this example i've added macOS to an existing rule for the Windows platform. Select the client apps, only Mobile apps and desktop clients are supported.
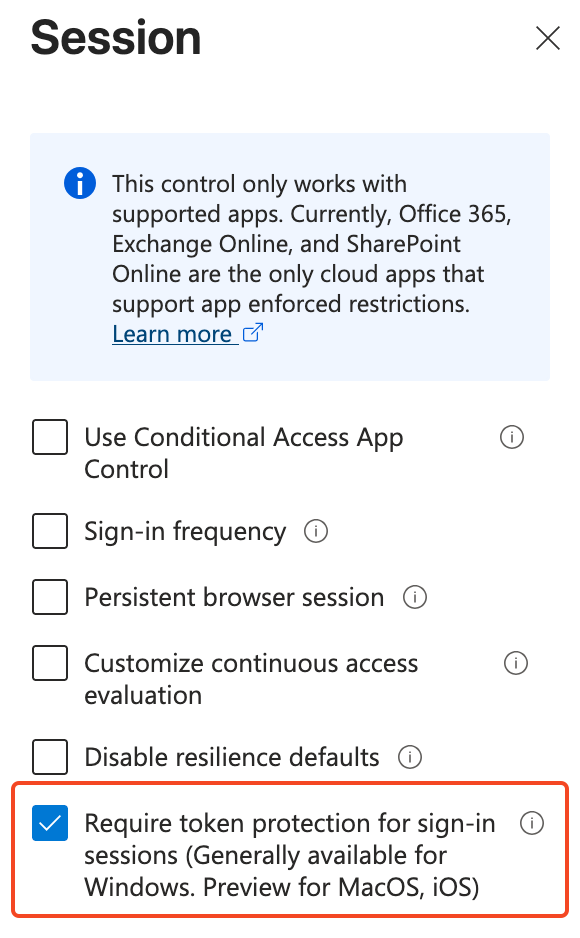
In the Session section for the CA rule, we need the enable the Require token protection for sign-in sessions. With this setting we wan't to enforce the use of a device where the logon credentials are protected, in this case the PSSO Secure Enclave method.
Logging & User Experience
With the CA rule in place that requires Token Protection we can check if the Token, which is used for authentication for several Microsoft services, is bound to the device. We need the head-over to the sign-in logs for the user using the macOS device to see if it's using Token bound for authentication.
From the Intune Portal
Users > Affected User > Sign-in Logs
Search for sign-in logs, when a device is managed with MDM and has the PSSO configuration, the user won't notice any changes. We can see in the logging that the resources is authenticated.
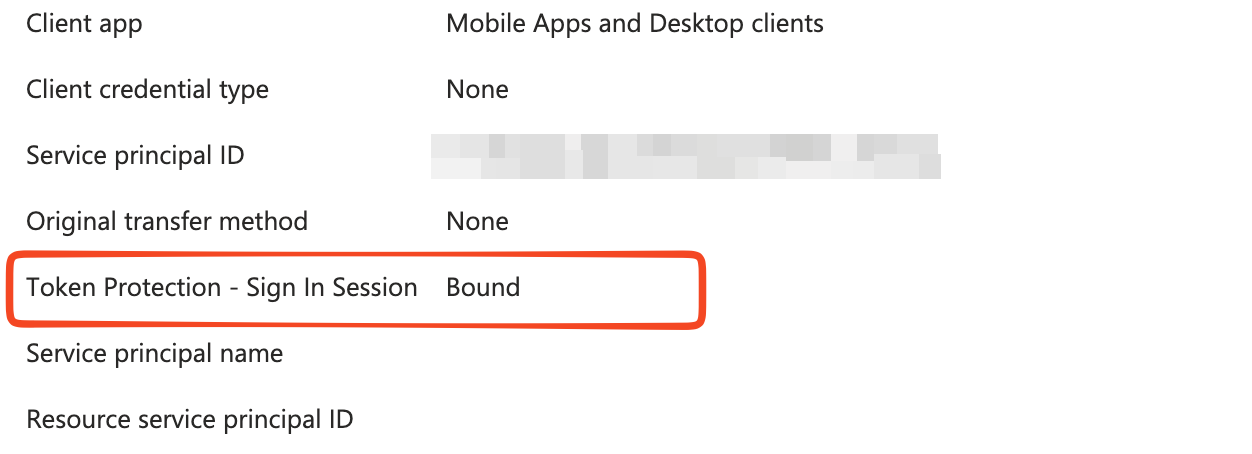
To find a correct resource i've search for the user sign-ins non-interactive. Look for the Token Protection - Sign In Session, we can see that this type is Bound.
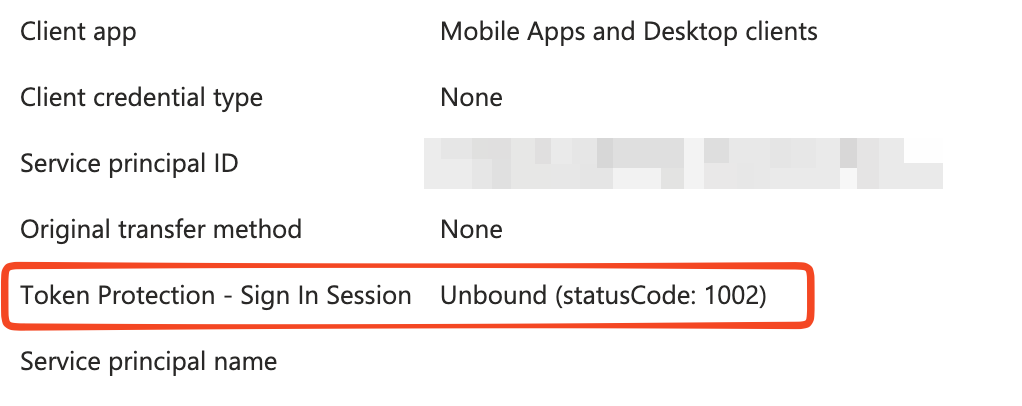
The real experience comes from a device where the user credentials aren't bound. When a user tries to authenticated to a supported services, they will get a notification depending on your CA rule to register their device, when a compliant device is required, or that a security policy is preventing access. In the logging we will see a similiar error but with a type of Unbound
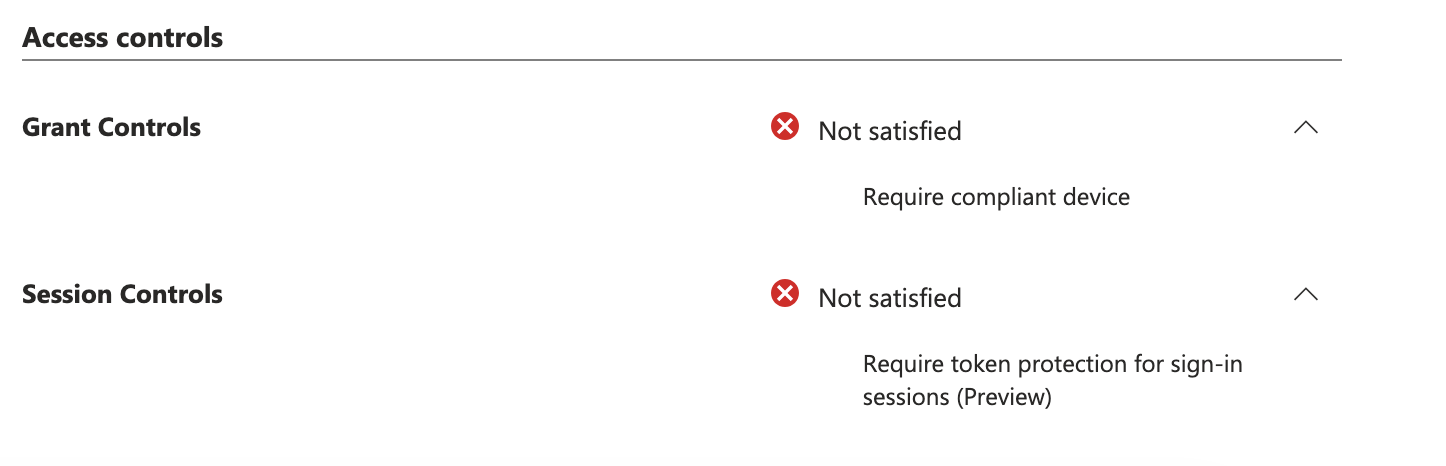
The Conditional Access rule will also show that authentication was blocked due to the session controls.
Recap
A Compliant device and MFA isn't sufficient now a days to conform that a users is trying to authenticate from a secure device. More phish-resistant methodes are needed. With a supported platform for macOS for Token Protection in Conditional Access and the capability for Platform Single Sign On with the Secure Enclave in macOS with Intune configuration policies, we have the tools to Safeguard our Tokens on our macOS devices.
